Exploit Windows 2000 machine using the Metaspolit
framework from the Kali Linux machine.
When the windows 2000
the machine came for public use, many vulnerabilities were identified. This was
caused by the number of vulnerabilities in IIS services. Many attacks came from
remote sources through the internet and there were critical flaws due to the
vulnerable encryption methods.
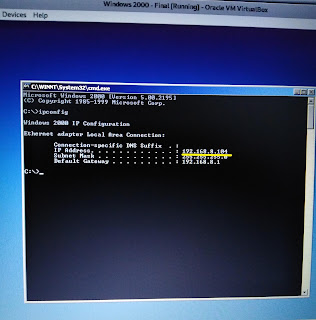
From this article how
the vulnerabilities of windows would be identified using Nessus, and exploit it
using Metasploit in kali machine will be described. To do it I am using my main
operating system (OS) kali and virtual machine windows 2000. For that IP range
of both machines should be in the same range to ensure those are in the
same network. Therefore network setting was fix as bridge adaptor in windows
virtual machine.
Then Nessus
vulnerability scanner is used to find the available vulnerability in Windows
2000.Start Nessus server,
sudo service nessusd start
sudo service nessusd start
Login to the Nessus
server. (If you login to the server using invitation code only, you can have
plugins for scanning.)
Select new scan à select advanced scan à then enter the name of the scan and victim machine’s IP
à save.
The Metasploit
framework has inbuilt exploits for predefined vulnerabilities. So here
Metasploit is used to exploit the victim's windows machine. Before starting, The Metasploit framework, apache2 server, and PostgreSQL database need to be
started.
To exploit the windows
2000 machine, the Metasploit console should be needed. Hence type,
Search for available
exploit for particular vulnerability.
Use the exploit to get
the attack shell
To see Show options for
attack,
Then set IP to exploit.
Finally, type exploit in
msf console
Exploit
Now we got access to
the windows machine successfully. Type pwd to see the
current directory.
To get command shell of
windows type
Here onwards we can
execute any command in windows 2000 machine to do several tasks.


















Comments
Post a Comment